Imagine walking through a factory floor, hearing the hum of machinery, watching sensors blink, and feeling the rhythm of seamless production. But beneath that calm surface, something sinister might be lurking-unauthorized devices whispering secrets, malware hiding in protocol traffic, or a rogue actor mapping your network’s weakest points.
“We help our OT customers across Central Europe protect their industrial networks. Often, vendors directly integrated into these networks unintentionally implement vulnerabilities, increasing risks from malware and cyber threats. Our diagnostics frequently uncover these issues, and we collaborate closely with customers to strengthen their cybersecurity defenses.”
– Cyber Security Technician, KFB Control
The truth? Your OT network knows more than it’s letting on. And if you’re not listening, you’re already behind.
The Silent Crisis in OT Security: “We Didn’t Even Know It Was There”
Operational technology environments are riddled with blind spots. Legacy systems, unpatched vulnerabilities, and shadow IoT devices create a perfect storm for cyberattacks. Consider this:
- 41% of industrial organizations can’t fully map their OT assets[1].
- 68% of OT breaches start with an attacker exploiting an asset the victim didn’t know existed[2].
But here’s the kicker: you can’t secure what you can’t see.
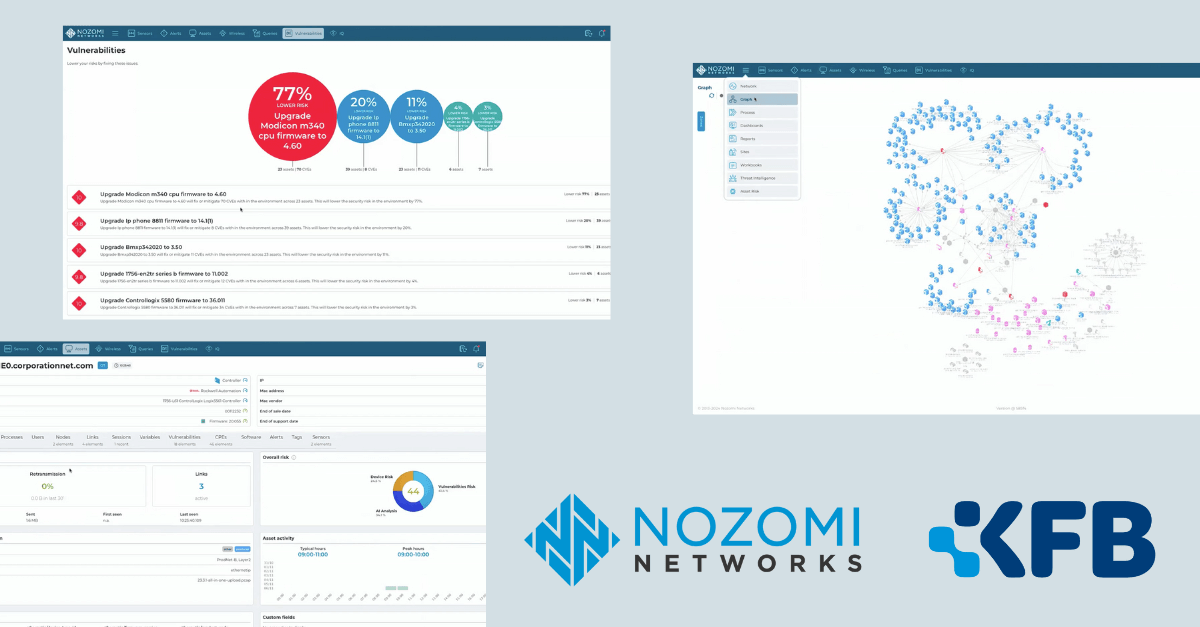
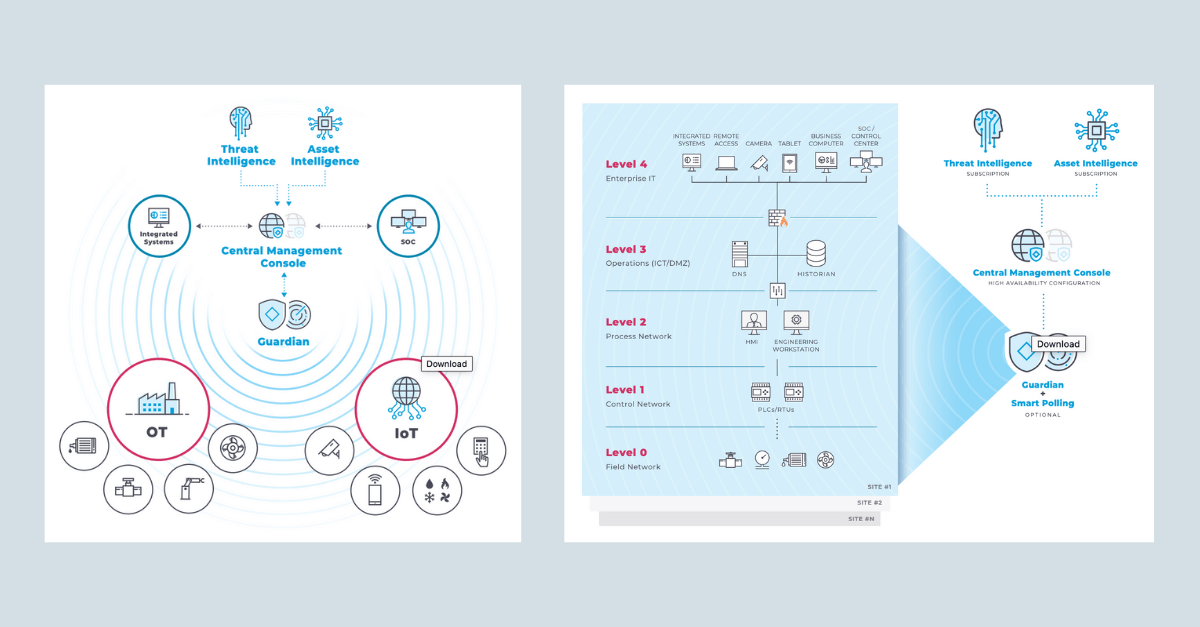
Nozomi Guardian: The Industrial Network’s Confessional
Meet the tool that’s turning OT security from a game of whack-a-mole into a strategic advantage. Nozomi Guardian isn’t just another monitoring solution-it’s your network’s truth-teller.
“I See Everything”
Guardian’s AI-driven asset discovery acts like an X-ray for your infrastructure:
- Automatically fingerprints every device, from decades-old PLCs to rogue IoT sensors[3].
- Maps communication flows between IT, OT, and cloud systems-exposing hidden dependencies that could cripple operations if compromised[4].
“We found devices we forgot we had-and vulnerabilities we didn’t know existed.”
– Global Pharma Company Case Study[5]
“I Know When Something’s Wrong”
While traditional tools miss subtle anomalies, Guardian’s machine learning baseline detects:
- Malware masquerading as legitimate Modbus traffic
- Unauthorized firmware updates that could brick critical machinery
- Data tampering in SCADA systems-before valves overheat or pipelines burst[6]
In one hospital network, Guardian flagged an insulin pump communicating with an unauthorized IP address-a potential life-or-death breach most tools would’ve missed[7].
The Provocative Truth: Your “Secure” Network Isn’t
Let’s cut through the hype:
- Firewalls alone are obsolete. Attackers breach Purdue Model layers via phishing engineers, not brute force[8].
- Air-gapping is a myth. 89% of OT networks have at least one unauthorized connection to IT or the cloud[9].
Guardian doesn’t just highlight risks-it forces a reckoning.
“What Happens Next Will Shock You”
Here’s where it gets interesting. When a major airport deployed Guardian:
- 90% faster threat detection by correlating CCTV feeds with network anomalies[10].
- $2M saved by preventing a ransomware attack targeting baggage systems during peak travel season[11].
But the real magic? Turning raw data into actionable defiance:
- Predict which legacy device will fail next (and why).
- Simulate attacks using PCAPs to train teams under fire[12].
- Enforce segmentation by auto-generating firewall rules when devices stray[13].
The Teaser Your SOC (Security Operations Center) Needs Right Now
What if you could…
- Spot a nation-state actor during their 72-hour reconnaissance phase?
- Predict equipment failures by analyzing network chatter?
- Prove compliance with IEC 62443 in 3 clicks?
Guardian does all this-and makes it look easy.
Don’t Let Your Network’s Secrets Become Headlines
The choice is stark:
- Keep flying blind until a $5M ransom note hits your HMI.
- Let Guardian expose the truth-and arm you to fight back.
“It’s like we’ve had the lights off for years. Guardian flipped the switch.”
– Energy Sector CISO[14]
Your OT network is talking. Ready to listen?
Sources:
- https://www.nozominetworks.com/products/guardian
- https://technicaldocs.nozominetworks.com/products/guardian/topics/intro/c_guardian.html
- https://assets-global.website-files.com/645a4534705010e2cb244f50/652f1295dd87704241398f17_Nozomi-Networks-Guardian-Sensor-Product-Overview.pdf
- https://www.ikarussecurity.com/wp-content/downloads/Nozomi-Networks-NIS-Compliance-Mapping-Guide.pdf
- https://www.nozominetworks.com/case-studies
- https://uploads-ssl.webflow.com/645a4534705010e2cb244f50/64c9ba7458652c3ccb920aef_Nozomi-Networks-Customer-Success-Brochure.pdf
- https://contentjourney.com/how-to-write-the-perfect-blog-post-title-with-examples/
- https://www.omnisend.com/blog/teaser-email/
- https://sellfy.com/blog/new-product-launch-email-subject-lines/
- https://securitybrief.com.au/story/nozomi-networks-named-leader-in-gartner-s-2025-quadrant
- https://www.nozominetworks.com/press-release/nozomi-networks-takes-home-repeat-win-at-coveted-global-infosec-awards
- https://www.orangecyberdefense.com/be/about-us/partners/nozomi-networks
- https://www.nozominetworks.com/resources/guardian-product-overview
- https://uploads-ssl.webflow.com/645a4534705010e2cb244f50/648c8503645576d81dca0db4_Nozomi-Networks-Top-Five-Global-Airport-Case-Study.pdf